VISULOX Policies - Overview
Overview
With VISULOX everything is controlled by VISULOX policies. A VISULOX policy has a VISULOX filter and depending of the object a time, when the policy is valid.
Policies are defined in the VISULOX Cockpit.
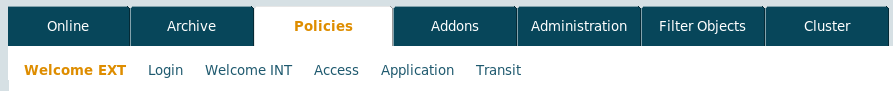
When a user is working under VISULOX, six policies are relevant and applied in an order.
Login and Access Policies are ordered from top to down. This means, the first matching policy is applied.
A new Login or Access Policy is always placed on top of the list of policies.
Every policy takes use of VISULOX Filters.
After a policy has been changed, it may last up to 15 seconds until the adjusted policy is available on all nodes in the VISULOX Cluster.
| Policy | General Function | Filter Criteria | Filter Time Frame |
|---|---|---|---|
| Welcome EXT | Controls the information seen by every user on the VISULOX PORTAL login page. In this case the user is not authenticated. | Access Point | yes |
| Login Policy | During authentication the policy defines the behaviour in the login process, like: Login allowed, Login with 2FA, etc. | Remote IP Access Point User/Group | no |
| Welcome INT | Controls the information seen by the authenticated user on his Workspace. | Access Point User/Group | yes |
| Access Policy | Controls if the authenticated user will have access to an application. | Remote IP Access Point User/Group Application | yes |
| Application Policy | Controls how VISULOX will control an application, e.g. with recording, with key stroke detection, etc. | Remote IP Access Point User/Group Application | no |
| Transit Policy | Controls the File Transfer into and out of the infrastructure | Remote IP Access Point User/Group | no |
Policies via Command Line Interface
- How to control internal messages from the command line
- How to control access from the command line
- How to control external messages from the command line
- How to control applications from the command line
- How to control login from the command line
- How to control groupaccess from the command line
- How to control File Transit Policy from the command line
- How to control groupaccess from the command line
- How to control File Transit Policy from the command line
- How to control applications from the command line
- How to control external messages from the command line
- How to control access from the command line
- How to control login from the command line
- How to control internal messages from the command line
- How to control access from the command line
- How to control groupaccess from the command line
- How to control external messages from the command line
- How to control File Transit Policy from the command line
- How to control internal messages from the command line
- How to control login from the command line
- How to control applications from the command line
- How to control access from the command line
- How to control File Transit Policy from the command line
- How to control applications from the command line
- How to control groupaccess from the command line
- How to control external messages from the command line
- How to control login from the command line
- How to control internal messages from the command line
- How to control external messages from the command line
- How to control login from the command line
- How to control File Transit Policy from the command line
- How to control internal messages from the command line
- How to control applications from the command line
- How to control access from the command line
- How to control groupaccess from the command line
